The internet has had a series of bad days over the last few months. In October, Microsoft 365 briefly went sideways in North America after a network misconfiguration disrupted access to Teams and Exchange Online before service recovered the same day. A few weeks later, Microsoft Azure suffered an outage after a faulty configuration change was pushed to Azure Front Door Configuration, affecting Microsoft 365, Xbox, and other services worldwide. Around the same time Amazon crashed, stating that an AWS disruption stemmed from a DNS automation bug associated with DynamoDB. This is an automated system that directs internet traffic that made a timing mistake, and that small glitch quickly snowballed and knocked parts of the service offline. Most recently, Cloudflare, a service many websites use to load faster and block bad traffic, went down, leaving millions unable to access sites and services. It’s no surprise that many business owners are now asking whether the cloud is still a safe choice for their business. Short answer: yes. For most small and mid-size companies, the cloud is still the safest, most cost-effective place to run everyday tools. It delivers enterprise-grade security, constant patching, and built-in resilience that would be expensive to match on your own. But “safe” doesn’t mean “never fail.”
In the early 2000s, tensions in the middle east were on the rise. Iran’s government had begun expanding its uranium enrichment capabilities, insisting it was for nuclear energy purposes. However many countries around the globe feared it was a coverup for a nuclear weapons program. Despite pressure from United Nations and the International Atomic Energy Agency, Iran continued to enrich uranium. Frustrations reached a fever pitch and it appeared a conflict was imminent, until a mysterious solution came from a completely unexpected source: the Stuxnet Computer Worm.

With growing concerns about data breaches and stolen credentials, many businesses feel pressured to invest in services that claim to scan the dark web for leaked information. But before committing resources, it's worth asking whether these tools actually provide meaningful information or if they are an unproductive expenditure. The dark web is a hidden part of the internet that you can’t reach with standard browsers or search engines. It operates using a system called Tor, which stands for The Onion Router. Tor keeps users anonymous by sending their internet traffic through several different servers around the world, encrypting the data each time. This makes it extremely difficult to trace who someone is or where they’re connecting from. Unlike regular websites that end in .com or .org, dark web sites usually end in .onion and require the Tor browser to access them. While some people use the dark web for legitimate reasons like protecting their privacy or avoiding censorship, it’s mostly associated with hosting illegal activities like online black markets, where stolen corporate data is sold.

When it comes to protecting your company’s infrastructure, two commonly used terms often cause confusion: vulnerability management and penetration testing. While they both serve the same purpose of keeping your data secure, they work very differently. Think of your company’s IT infrastructure like a museum that stores priceless artifacts. To keep it secure, you wouldn’t just install locks and hope for the best. You’d want to routinely check those locks, ensure windows are closed properly, and perhaps even hire someone to test how easy it is to break in. This is basically the difference between vulnerability management and penetration testing.

Three things in life are certain: death, taxes and the persistent threat of cyberattacks. There are many layers of defense in the onion of cyber security, but at the helm is your firewall. Traditionally firewalls have always been the piece of hardware acting as a barrier between your office network and the wilds of the internet. Then in 2020 the way we work was transformed forever by the global pandemic. Nearly a third of the workforce transitioned to remote, leaving offices empty. Many employees continue to work in non-traditional spaces to this day. How can we defend them against cyberattacks if they are outside the protective reach of an on premise firewall? A firewall is a network security device or software that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Think of it as a moat with a bridge and a guard shack that surrounds a castle. The guards and the moat are the firewall, acting as a barrier and between a trusted internal network (the castle) and untrusted external networks (random people trying to get in), helping to prevent unauthorized access to and from the castle while allowing legitimate traffic to pass through. The outside forces have to “check in” with the guards before they can cross the moat and access the castle.

You may have heard recently that the FBI and Cyber Security and Infrastructure Security Agency are recommending cell phone users use end to end encryption when sending text messages. Why are they doing this and how does it affect you and your business? In December of 2024 authorities revealed that Chinese hackers have breached at least 8 major telecom network infrastructures, including those of Verizon and AT&T. Known as Salt Typhoon, the nefarious actors used a “back door” that is used by U.S. foreign intelligence surveillance systems (yes that’s legal wiretapping). Senior officials within the US Government have admitted the hackers have had access since summer of 2024. It appears that they focused heavily on users in the Washington DC area.

Imagine a virus infecting over 85 million Android phones without anyone catching on. Believe it or not, this really happened in 2016! How could a virus be so easily distributed without human intervention? The HummingBad virus was a persistence rootkit, which is a very smart and nasty virus. It is difficult to find and even more difficult to remove. They embed themselves within the system without the users knowledge and they are designed to hide themselves and their activities, even from security software. A rootkit will take over an infected system on its own, or if it cannot gain root access, it will push a fake update prompt, tricking the user into installing. Once the malware has control of the device, it begins downloading and installing apps, and the lucrative business of conning users begins. The HummingBad virus was designed to click on the ads within the apps to generate advertising revenue. This inflated ad click and view counts, allowing the attackers to earn more revenue without actual user engagement. The malware also promoted and installed additional malicious
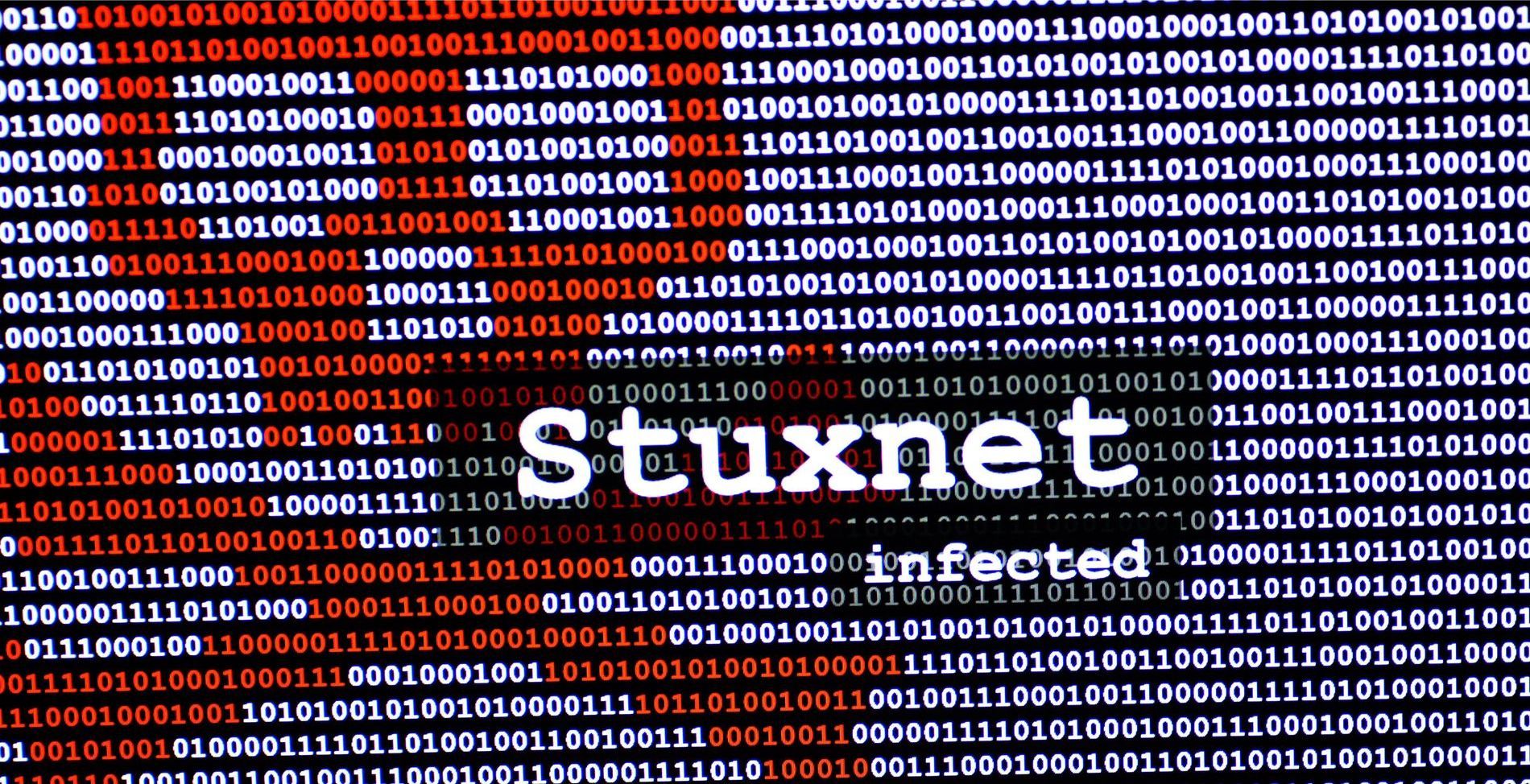
Picture this: You're witnessing the culmination of years of hard work as the first humans are about to land on the moon's surface. Suddenly, the moment is shattered by blaring alarms. This exact scenario unfolded during Apollo 11's momentous moon landing. Luckily, Margaret Hamilton and her accomplished team of NASA engineers had meticulously readied themselves for any imaginable situation. Margaret Hamilton is best known for her work on the Apollo moon missions. In the 1960s, she was the lead software engineer for the Apollo Guidance Computer, which was the specialized computer that was responsible for guiding the Apollo spacecraft to the moon. Her job was to make sure the system was reliable, efficient, and could handle the complex calculations needed for space travel. During the Apollo 11 mission, Margaret Hamilton's team faced a critical situation where the computer system on the lunar module experienced an overload during the landing. This overload was caused by an unexpected increase in processing demands as the computer tried to do numerous tasks at the same time.

In the headquarters of Cloudfare, a California based tech company, there is a most wonderous wall of mystery. Towering over the entrance, lies wall of around 100 brightly colored lava lamps. While they may be enticing to the eye, these lava lamps actually have a very important job in the security department. Cloudflare provides content delivery network services and DDoS mitigation, and they are known for using lava lamps in their offices as part of its encryption process. The concept is based on a method called "entropy source," which helps generate truly random numbers for encryption keys. Entropy sources are used in cryptography to generate randomness for various security-related processes, such as encryption key generation and secure communication protocols. Entropy, in this context, refers to the unpredictability and randomness of data, which is crucial for ensuring security and preventing cryptographic attacks.
Earlier this month a peculiar story began circling the internet: a Denial of Service attack was being implemented at the hands of millions of Smart Toothbrushes. This turned out to be false information, but could it actually happen? During a Distributed Denial of Service (DDoS) attack, a large number of compromised or infected devices, often referred to as bots or zombies, are used to flood a targeted website, server, or network with an overwhelming amount of traffic. This flood of traffic is intended to interrupt the target's normal operation, making it inaccessible to legitimate users. The threat actor can use literally any device with an internet connection – so yes, a smart toothbrush could contribute to taking down the internet! These attacks can take years of effort on the hackers part before they come to fruition. The hacker gains control of hundreds if not thousands of devices over time. They connect them to create a botnet, and use specialized software or scripts to instruct the botnet to send a large volume of fake traffic to the target. This surge in traffic can overpower the target's bandwidth, server capacity, or other resources, causing it to be